Max Knape & Albin Eriksson · 28 April 2026 Läs på svenska
The Future of Customer Risk Classification: Separating Risk Assessments for ML, TF, and Sanctions
A customer is classified as high risk. But high risk of what? Money laundering? Terrorist financing? Sanctions exposure? Many of today’s customer risk classification models simply don’t provide an answer. Customers are assigned a single aggregated risk score, while the underlying drivers of that risk remain unclear. This leads to inefficiency, misaligned actions, and increasing difficulty in meeting regulatory expectations.
Regulatory developments: Increasing requirements on risk differentiation
Regulation within AML/CTF and sanctions is evolving toward a more explicit separation of risk types.
It is already well established that business-wide risk assessments must clearly distinguish between money laundering and terrorist financing risks, and that transaction monitoring should include dedicated scenarios for each risk. Furthermore, supervisory authorities such as Finansinspektionen have intensified their focus on how institutions identify and manage terrorist financing and sanctions risks.
Requirements will tighten further. Under the new EU regulation Anti-Money Laundering Regulation (AMLR), entering into force in summer 2027, institutions will also be required to assess sanctions risks and the risk of sanctions circumvention within their business-wide risk assessments. In addition, the European Banking Authority’s guidelines on sanctions make it clear that customer due diligence measures must explicitly take sanctions risk into account.
How do the risks differ?
The regulatory shift toward risk differentiation reflects the underlying reality: risks for money laundering, terrorist financing and sanctions breaches differ fundamentally in both purpose and manifestation. As a result, they require entirely different detection approaches.
Different objectives
- Money laundering (concealing origin):
Focused on hiding where funds come from. Proceeds of crime are layered through complex financial structures to appear legitimate. - Terrorist financing (concealing purpose):
Focused on hiding how funds will be used. Amounts are often small and may originate from legitimate sources - the illicit element lies in the intended use. - Sanctions breaches (concealing the actor):
Often focused on hiding who is involved. The objective is to circumvent restrictions by obscuring links to specific individuals, entities or jurisdictions.
Different patterns in data
The differences in purpose translate into fundamentally different behavioral patterns in customer data and transactions:
- ML risk (inconsistency and complexity):
Typically identified through deviations in the customer profile - for example, inconsistencies between industry classification, revenue, transaction behavior and geographic exposure, or unnecessarily complex ownership structures. - TF risk (context and intent):
Less about complexity and more about context. Risk often arises from a combination of customer type, activity and geographic exposure - such as non-profits operating in or sending funds to regions near known conflict zones. - Sanctions risk (structured linkages):
Primarily driven by direct or indirect connections in structured data - such as links to jurisdictions associated with sanctions circumvention, or to listed individuals and entities identified through attributes like citizenship, beneficial ownership, ownership structures, address and tax residency.
The consequence
The risks do not just differ in theory - they manifest differently in practice. A risk classification model that fails to capture and handle these differences in a sophisticated way is likely to miss what actually drives risk for a given customer.
The need: A differentiated risk classification model
To enable proportionate and effective customer due diligence, institutions need a risk classification model that can distinguish and quantify money laundering, terrorist financing, and sanctions risks separately.
Whether implemented as standalone models or as modular components within a broader framework, the principle remains the same: a customer’s risk profile cannot be reduced to a single aggregated score without losing critical information.
When a customer is classified as high risk, analysts must be able to answer a simple question: What is driving the risk? Is it money laundering, terrorist financing or sanctions?
Without this clarity, institutions risk applying the wrong controls - or failing to apply the necessary controls where they matter most.
Yet many traditional approaches rely on the blunt assumption that a given risk factor carries the same weight regardless of whether it is assessed from an ML, TF or sanctions perspective. This forces aggregation into a single, non-specific risk score.
Why risks must be separated
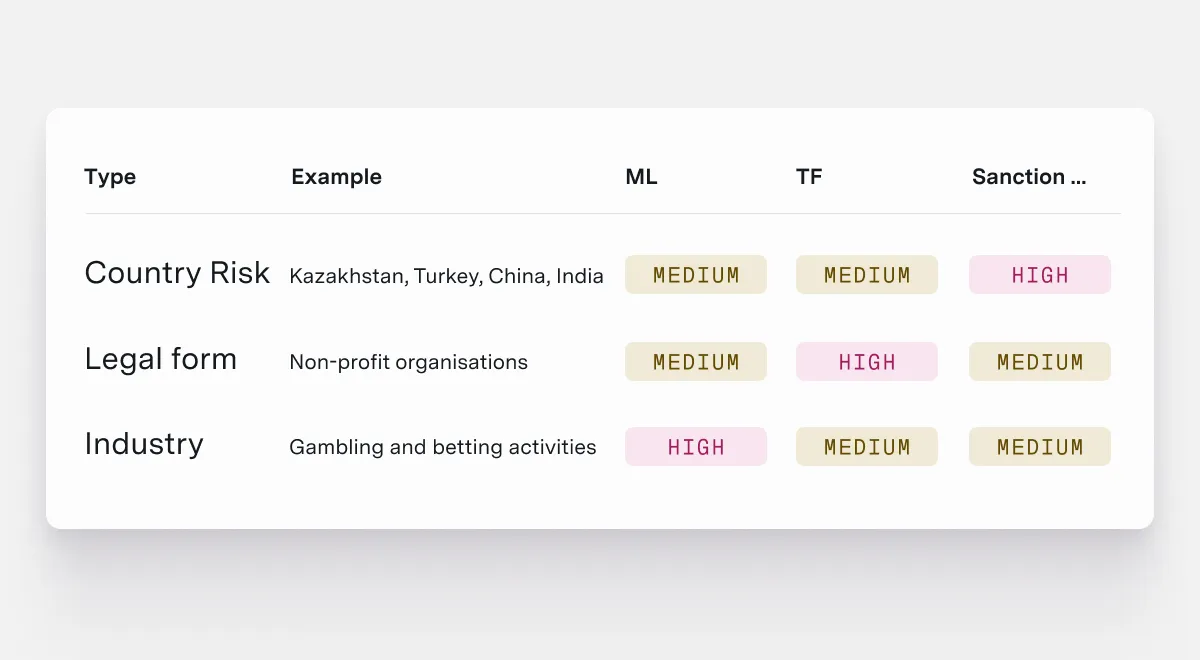
- A country may present high sanctions risk (e.g. due to risks of circumvention), but only medium money laundering or terrorist financing risk. Examples include Kazakhstan, Turkey, China, and India.
- Certain entity types, such as non-profits, may carry high risk of terrorist financing but not elevated money laundering or sanctions risk.
- Specific industries, such as casinos and gaming, may represent high money laundering risk but lower terrorist financing and sanctions risk.
The problem with traditional models
In many existing systems, these risk factors can only be assigned a single risk rating (low, medium or high). This leads to two problematic outcomes:
- Overgeneralisation of risk:
Parameters are set to “high risk” across the board for all risk types, resulting in large volumes of customers being flagged as high risk regardless of the actual risk. - Underestimation: of risk
To avoid excessive false positives, risk levels are lowered instead. For example, risk for sanctions circumvention may be overlooked, leading to countries like India and China being incorrectly classified as “medium risk”.
Consequences and business impact
A framework that cannot differentiate between risk dimensions can lead to two serious consequences:
- Inefficiency and misaligned controls:
Overgeneralisation of risk results in incorrect high-risk classifications (too many high risk customers), undermining the risk-based approach and leading to inefficient and inappropriate actions. - Missed high-risk customers:
Customers with genuine risk exposure - such as sanctions circumvention or terrorist financing - may be incorrectly classified as low or medium risk, resulting in critical controls not being applied.
The future of risk classification models: Operationalising differentiation
Dynamic risk factors at the core
Regardless of system architecture, it is essential that the same risk factor can carry different weights depending on the risk dimension being assessed.
A single parameter - such as a country, entity type or industry code - must be able to take on different values depending on the risk dimension being assessed. For example, a specific country may represent:
- High sanctions risk
- Medium ML risk
- Low TF risk
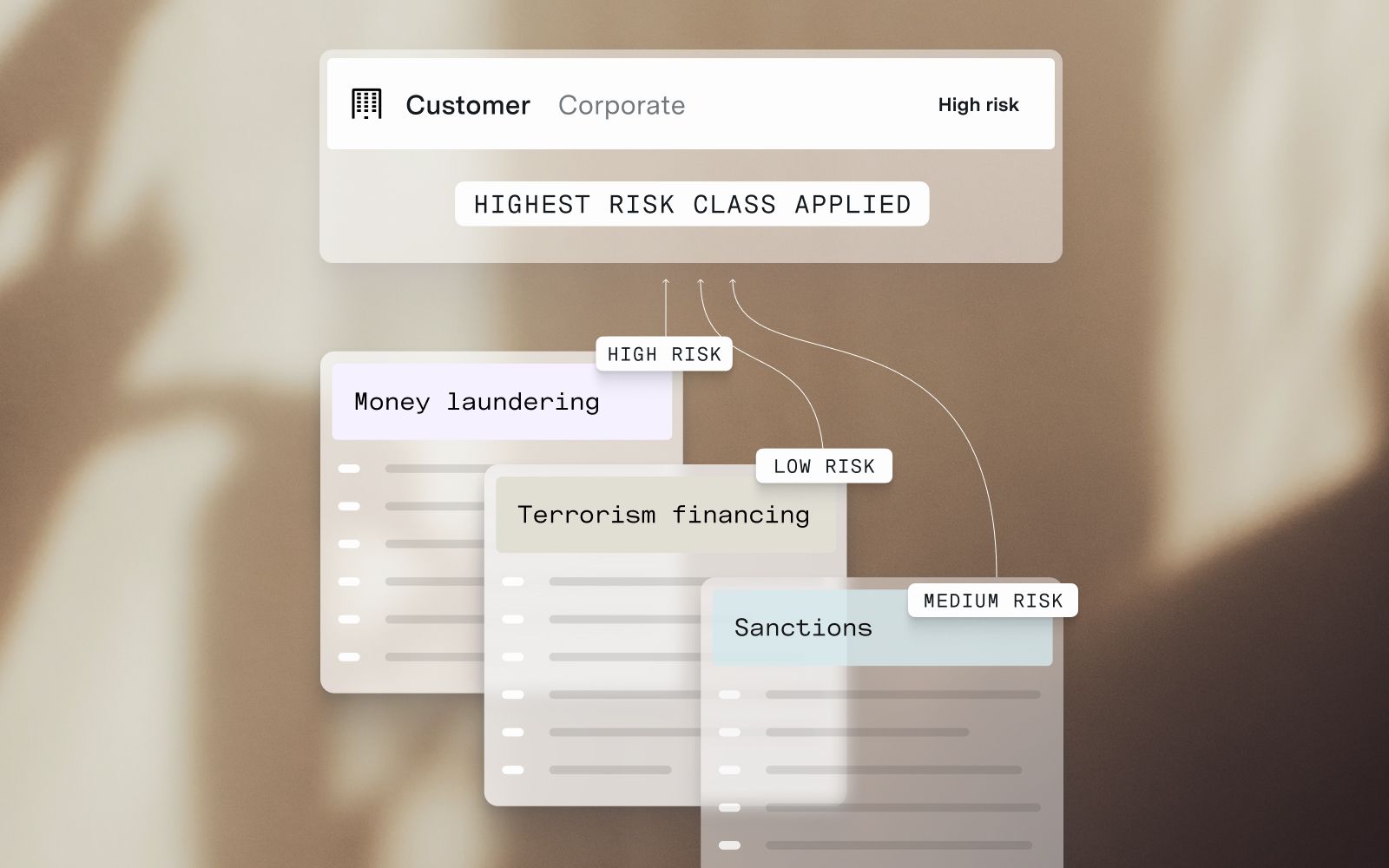
Separate risk classifications
By separating calculations, each customer can be assigned three distinct risk ratings.
Operationally, the system can still use the highest of these to flag the customer as high risk at an overall level - ensuring appropriate escalation and resource allocation.
The key difference is traceability. Analysts can immediately understand why a customer is high risk and identify the specific dimension driving that classification. This eliminates unnecessary manual work and ensures that the right controls are applied.
This differentiation also enhances transaction monitoring. Instead of relying on a single, blunt “overall risk”, thresholds for specific scenarios - such as terrorist financing - can be calibrated precisely based on the customer’s actual risk of terrorist financing.
Summary
Regulatory developments clearly point toward an increasing need to differentiate between money laundering, terrorist financing and sanctions risks.
Inflexible models that aggregate these risks into a single score are likely to become both inefficient and non-compliant over time.
By implementing models that enable separate risk assessments, institutions can:
- Improve the precision of risk classification
- Ensure the right controls are applied
- Meet evolving regulatory expectations
The future of risk classification is not about measuring more risk - it is about measuring the right risk, in the right way.